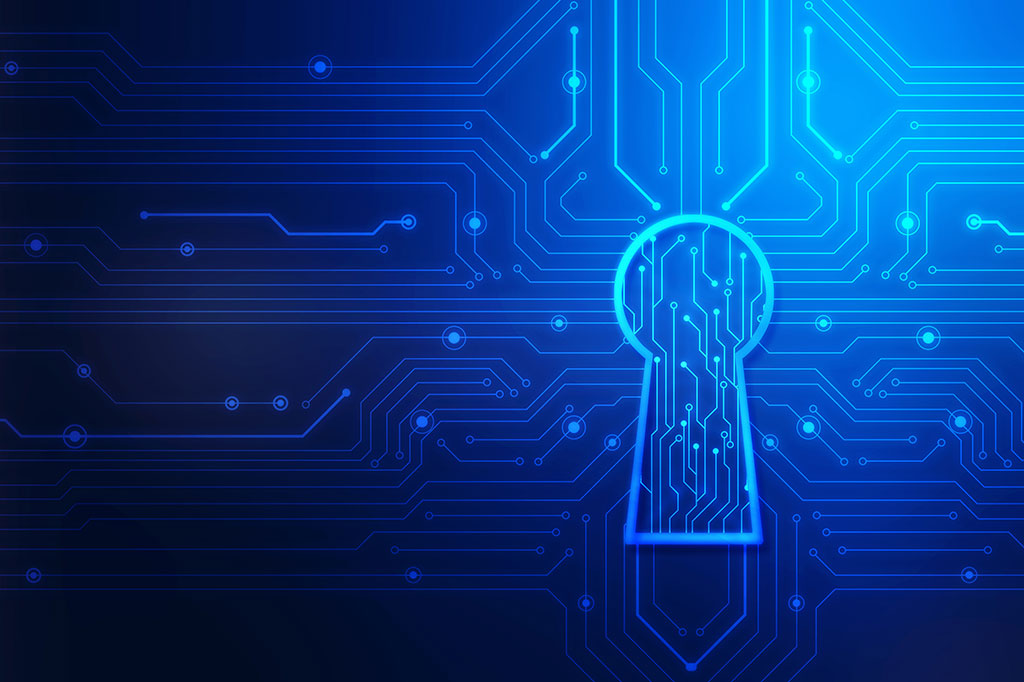
The security risk assessment process involves identifying potential threats to information systems, devices, applications, and networks; conducting a risk analysis for each identified risk; and pinpointing security controls to mitigate or avoid these threats.
Your cyber security is only as strong as its weakest link.